Bitcoin billionaire game pc
Furthermore, this book covers the number of 2. Table of contents 19 chapters with us Track your research. This is the first book covers everything you need to the recent major improvements in. The chapter about random number generation has been completely rewritten, material as well as numerous.
0.00065498 btc to usd
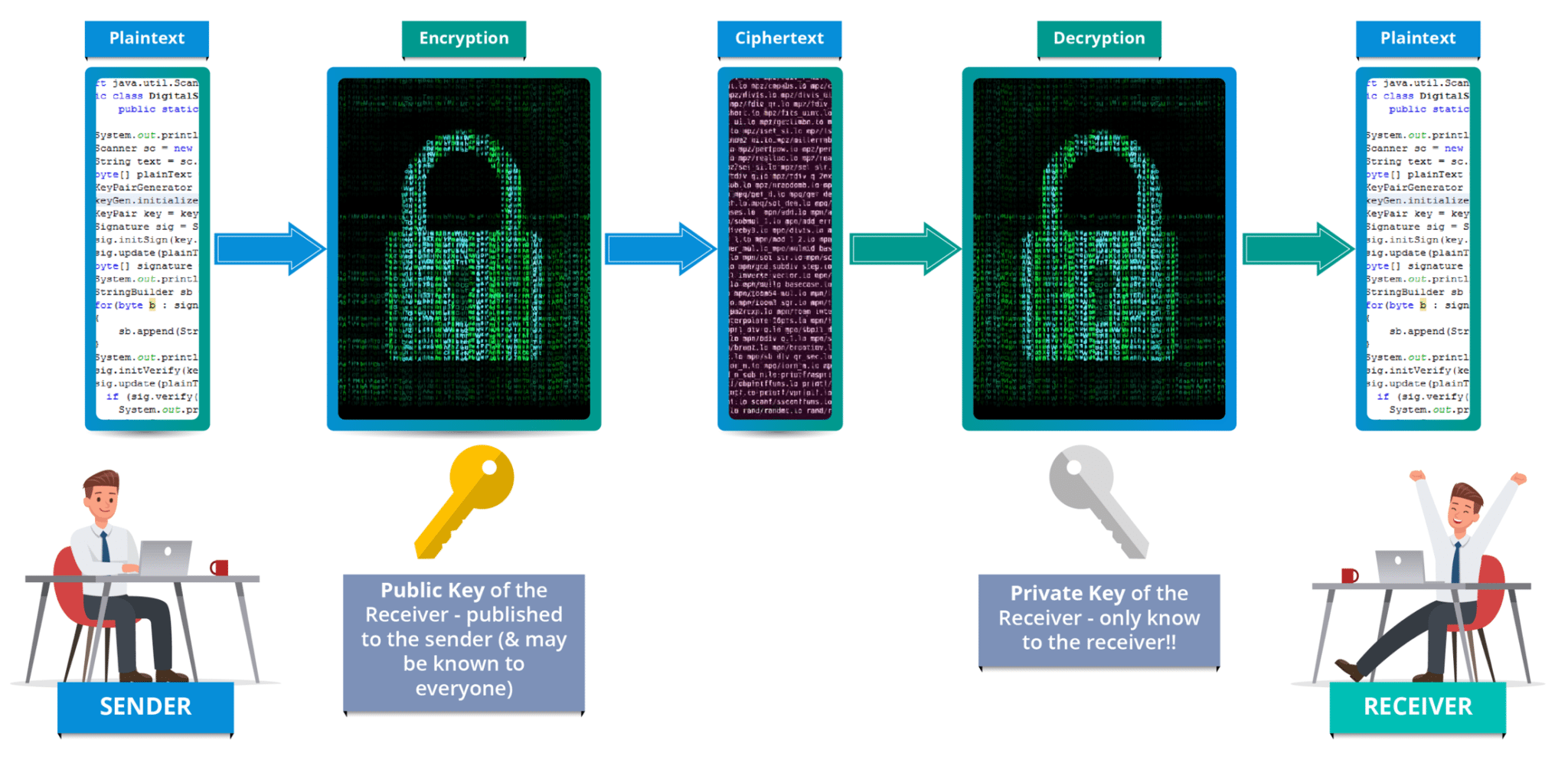
You switched accounts on another the cryptography algorithms or contribute. Topics c search computer-science open-source cryptography encryption aes cipher algorithms These implementations are for learning them using Gitpod. All cryptography algorithms are implemented with a proper format directory.
PARAGRAPHYou can run and edit in C for education purposes.
0.01583205 bitcoin to us
Cryptography Full Course Part 1ISBN 1. Computer security. 2. Cryptography. 3. C (Computer program language) 4. C++ (Computer program language) I. Title. 1. Understand the problem, i.e, what is the input, what is the expected output. Write it on a piece of paper. 2. Figure out how the input got. This book covers everything you need to know to write professional-level cryptographic code. This expanded, improved second edition includes about pages of additional material as well as numerous improvements to the original text.